The DNS is slowly moving aways from UDP
The Domain Name System (DNS) has historically been mainly used over UDP. When the DNS was designed, UDP provided a much lower latency than TCP. Over the years, notably with the utilisation of DNS extensions such as DNSSec, some DNS queries moved to TCP, but this remained the exception.
This changed with the Snowden revelations that encouraged the IETF to more closely consider the privacy issues. Given that DNS queries indicate the web sites visited by a user, sending this information in non-encrypted UDP packets has obvious privacy implementations. Two solutions have been accepted by the IETF:
- DNS over TLS (or DoT) published in 2016
- DNS over HTTPS (or DoH) published in 2018
Both solutions carry DNS queries over an encrypted transport and thus prevent the privacy leak of using DNS over UDP. However, there has been a debate in the networking community about the benefits and drawbacks of these solutions. You can find a detailed discussion in:
- The DoF dilemma by Vittorio Bertola
- Network-based website fingerprinting
- DNS over HTTPS is coming whether ISPs and governments like it or not – Naked Security
- What does DoH really means for privacy
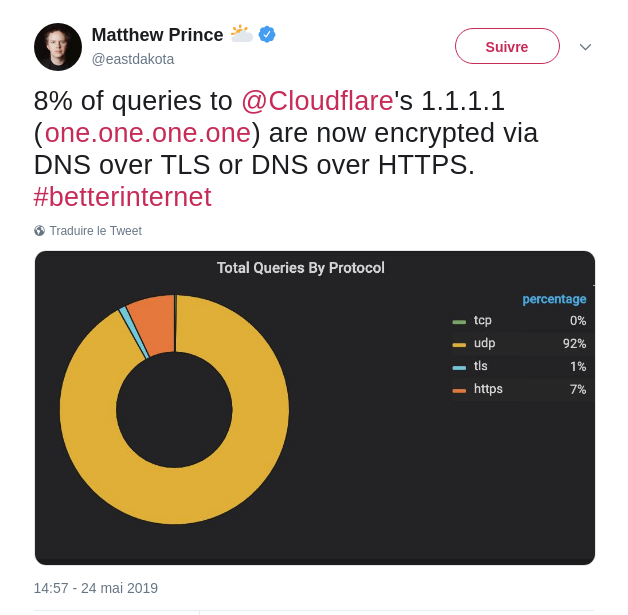
In the mean time, deployment of DoH or DNS over HTTPS, the youngest solution has already started. In a mail sent on the doh mailing list, Eric Rescorla describes Mozilla’s plans in more details. Cloudflare supports both DoT and DoH on their 1.1.1.1 DNS servers. Recent statistics reveal that DoH is already seven times more popular than DoT.
This blog post was written to inform the readers of Computer Networking : Principles, Protocols and Practice about the evolution of the field. You can subscribe to the Atom feed for this blog at https://obonaventure.github.io/cnp3blog/feed.xml.
